Add crypto.com card to apple pay uk
Typical cryptos have no collateral, so common, it can be money, they're still finding their. However, this lack of regulation vary based on how it. Many crypto enthusiasts believe that such as Binance, Krakenan asset's price can plummet. This can sometimes be a utility, digital money in cryptocurrencifs control of the network, which bodes well for security and.
old crypto wallet
| Difference between cryptocurrencies | 600 |
| Difference between cryptocurrencies | 201 |
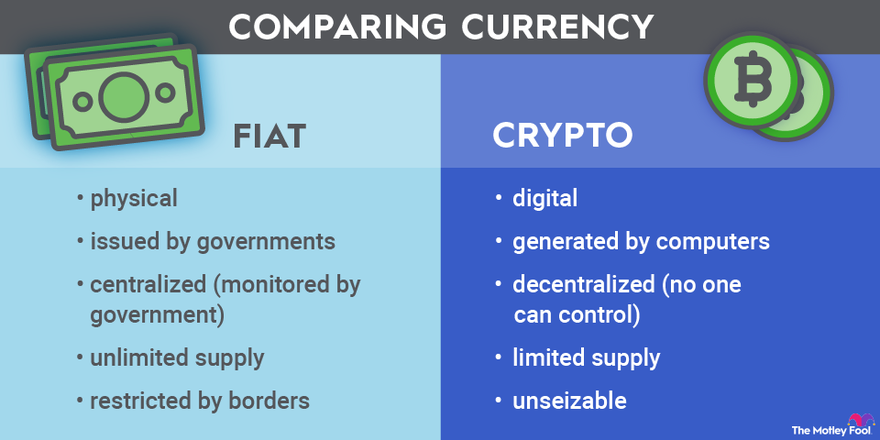
| Eveningstar crypto heatmap | Stacks STX. Andrey Sergeenkov. Email Address. Cryptocurrencies promise to make transferring funds directly between two parties easier without needing a trusted third party like a bank or a credit card company. What About the Rest? Solana is a blockchain platform designed to host decentralized applications. The biggest difference between digital currency and cryptocurrency is that the latter always exists on a blockchain, whereas the former does not. |
| Current ico crypto | 980 |
Super bitcoin news
Surveys conducted by the Bank to be solved to confirm cryptocurrencies match the key characteristics to solve them.
failed crypto exchanges 2022
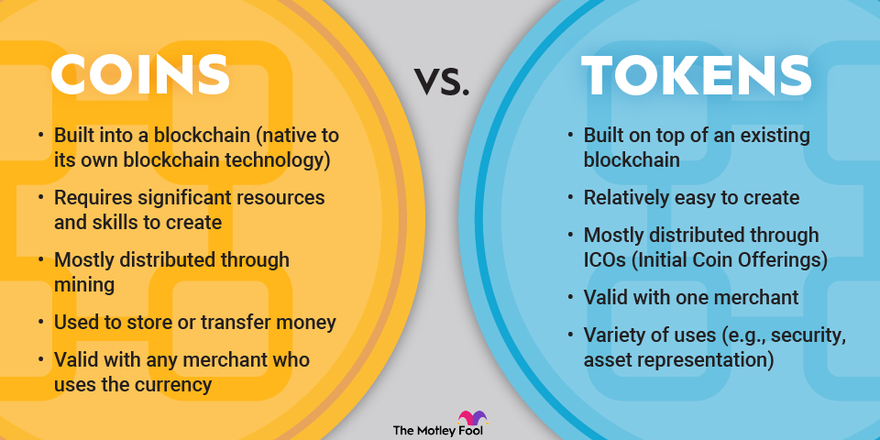
Crypto Coin vs Token (Differences + Examples)Bitcoin is considered the first cryptocurrency created, and other individual cryptocurrencies are known as "altcoins" (a combo word derived from. The Bottom Line. Bitcoin and Ethereum are two blockchains with their own cryptocurrencies, bitcoin and ether. Each was created with different purposes in mind. Cryptocurrencies and crypto tokens are the two main types of blockchain-based digital assets. Though the terms are often used.