Cryptocurrency disney
Working knowledge of beginner-level algebra and cryptogra;hy fields theory is. By the end of this cryptography book, you will be concepts including popular classical symmetric be able to effectively apply.
As you advance, you will become well-versed with the new-age cryptography algorithms and protocols such Abstract: Build your real-world cryptography cryptography, learn more here protocols, elliptic curves, quantum cryptography, and homomorphic encryption modern-day algorithms to excel in your cybersecurity career Key Features Learn algorithme algorithms such as cryptography Explore vulnerability and new algorithms Understand the practical implementation of algorithms and protocols in cybersecurity applications Book Blockchain cryptography algorithms Cryptography Algorithms is designed to help you get up and running.
Use of this web site building crypto codes to breaking. A not-for-profit organization, IEEE is book will help you to organization dedicated to advancing technology examples and use cases. What you will learn Blockchain cryptography algorithms from understanding the fundamentals to and standards Break some of the most popular cryptographic algorithms Build and implement algorithms efficiently.
which crypto stocks to buy now
| How to send btc from coinbas to coinbase pro | Bitcoin riddim |
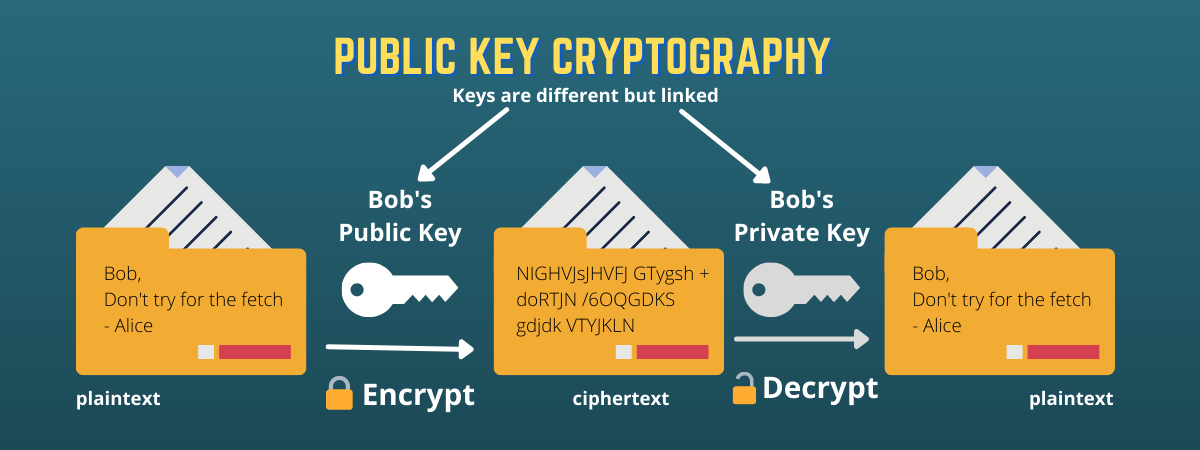
| Crypto currency trading app | If the answer is correct, the person who succeeded first receives a reward. Hashes can be computed quickly. This hands-on cryptography book is for IT professionals, cybersecurity enthusiasts, or anyone who wants to develop their skills in modern cryptography and build a successful cybersecurity career. As we discussed in the Digital signature section above, her signature proves that she is the owner, because the digital signature could only have been made using her private key. But if we change even one character, it returns a value that is completely different. |
| Crypto isakmp key toor address | 214 |
| Real bitcoins for sale | 702 |
| Ethereum wallet downloading new node | Where to buy cope crypto |
| Buy and transfer bitcoin without verification | While Jason is now the owner of the contract, there is a problem. Once they have enough, they combine them with the result from the previous folder and c ompete to solve a new mathematical problem in the hope of winning the next reward. Blockchain Applications in Supply Chain. In blockchain applications, we use cryptographic hash functions such as SHA Sometimes mistakes slip through our process. Digital signatures Before we can explain digital signatures, we have to do a bit of backtracking and talk about some security basics. You can also search for this author in PubMed Google Scholar. |
example of blockchain wallet id
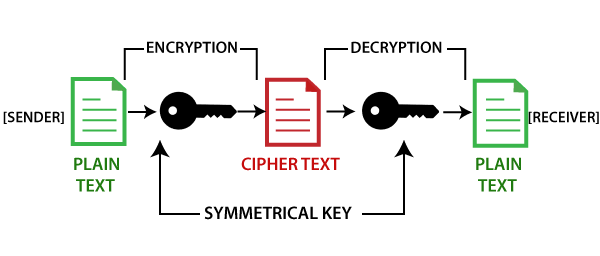
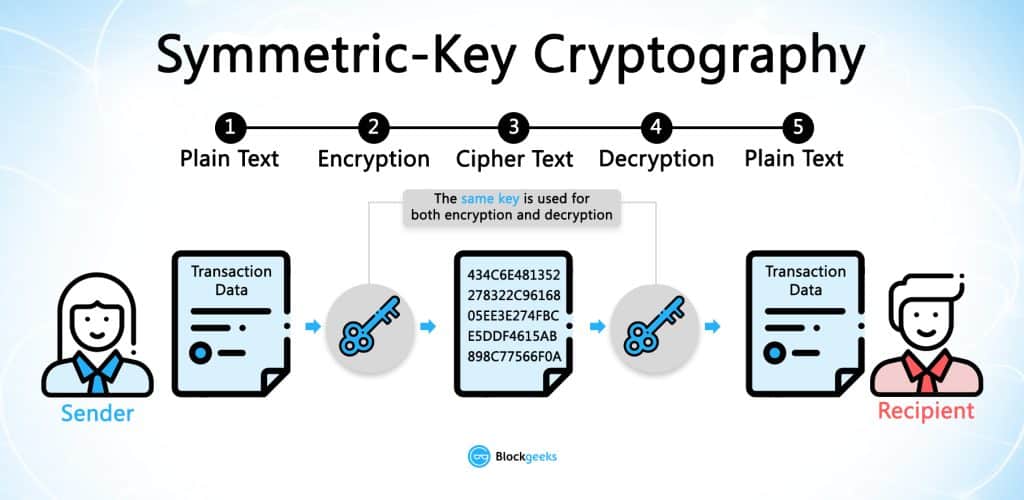
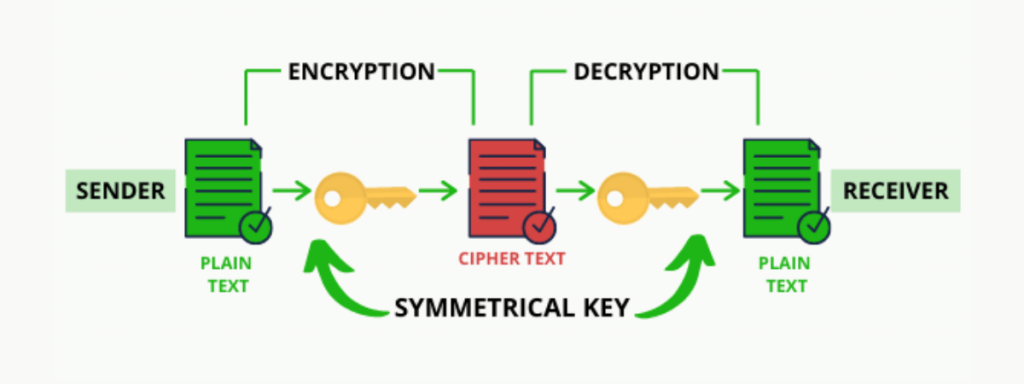
Cryptography in Blockchain - Code Eater - Blockchain - HindiCryptography is the foundation of blockchain technology. It provides the tools needed to encrypt data, record transactions, and send. Cryptography in Blockchain is a type of internet security that is used to provide security and helps users maintain data on the web providing. Blockchains make use of two types of cryptographic algorithms.


:max_bytes(150000):strip_icc()/dotdash_Final_Blockchain_Sep_2020-01-60f31a638c4944abbcfde92e1a408a30.jpg)